In 2026, protecting your primary email from spam, data breaches, and tracking is non-negotiable. Temporary email tools are your first line of defense, offering disposable addresses for sign-ups and verifications. This guide cuts through the noise to review the most reliable, private, and user-friendly services. We evaluate them on speed, security, and features to help you choose the perfect tool for your digital privacy needs.
Remember that sinking feeling? You sign up for what seems like a useful online tool or a one-time discount, carefully using your main email. Weeks later, your inbox is buried under a relentless tide of promotional spam. Your data has been sold, shared, or leaked, and you’re left cleaning up the digital mess. In 2026, this isn’t just annoying—it’s a serious privacy and security risk. The solution? A temporary email address. But with countless options popping up, which ones actually deliver on their promises of privacy, reliability, and ease of use? This is your definitive, no-fluff guide to the best temp email tools for 2026.
We’ve moved beyond the simple, bare-bones disposable inboxes of the early 2010s. Today’s leading tools are sophisticated privacy guardians, often packed with features that rival permanent email services—without the long-term commitment or baggage. They’re not just for avoiding spam; they’re a critical tool for managing your digital footprint, testing services, and safeguarding your identity. Forget everything you thought you knew about “disposable email.” Let’s dive into the tools that define the category in 2026.
Key Takeaways
- Temp emails are essential privacy shields: They prevent spam, data harvesting, and credential stuffing attacks on your primary inbox by providing a sacrificial address for one-time use.
- Not all disposable mail services are equal: Key differentiators include inbox retention time, domain variety, browser extension support, and whether they require registration.
- Look for advanced privacy features: The best 2026 tools offer end-to-end encryption for the temporary inbox, no-logs policies, and built-in ad/tracker blockers.
- Integration is key for usability: Top tools seamlessly integrate with browsers via extensions or mobile apps, allowing one-click generation and auto-fill of temp addresses.
- They are for verification, not critical communication: Use temp mail for account sign-ups, download access, and forum registrations, but never for banking, primary accounts, or important correspondence.
- The future is AI-powered management: Emerging tools use AI to categorize incoming temp emails, auto-delete after use, and even suggest when a temp address is no longer needed.
- Legal and ethical use matters: These tools are for personal privacy, not for fraud, bypassing bans, or malicious activity. Always respect a website’s Terms of Service.
📑 Table of Contents
Why a Temporary Email Isn’t Just for Spam Anymore
Let’s clarify the core mission first. A temporary or disposable email service provides you with a random, public inbox address that lasts for a short, predefined period—usually 10 minutes to 48 hours. The primary purpose is to act as a buffer between your real identity and a website or service you don’t fully trust or only need once.
The Modern Privacy Imperative
In 2026, data is currency. Every online form filled with your primary email is a data point sold to advertisers, aggregated by data brokers, and potentially exposed in a breach. Using a temp email severs that link at the source. It’s a proactive privacy measure, not a reactive spam filter.
Beyond Spam: Security & Testing
Consider this: you’re trying a new SaaS platform. Do you really want to give it your work email, potentially triggering internal security alerts? A temp email lets you test freely. For developers and QA testers, it’s invaluable for creating multiple test accounts without managing a zoo of real inboxes. It also thwarts “credential stuffing” attacks, where hackers use breached email/password combos on other sites—your temp address is a dead end for them.
The Ethical Boundary
A crucial note: these tools are for legitimate privacy protection and testing. Using them to create accounts on platforms that explicitly ban disposable emails (like many social media or banking sites) violates their Terms of Service. The goal is to protect *your* data, not to circumvent *their* rules fraudulently. Use responsibly.
How We Evaluated the Best Temp Email Tools for 2026
Not all temp mail services are created equal. Some are slow, some are filled with intrusive ads, and some simply vanish when you need them most. Our evaluation for 2026 focused on five critical pillars:
Visual guide about Best Temp Email Tools for 2026
Image source: techgrapple.com
- Speed & Reliability: Does the inbox load instantly? Do verification emails arrive within seconds, or do you miss a time-sensitive code?
- Privacy & Security: Is there a no-logs policy? Is the connection HTTPS encrypted? Does the service sell your activity data?
- User Experience (UX): Is the interface clean? Is there a browser extension or mobile app for one-click generation? How many clicks to copy the address?
- Feature Set: Inbox retention time, custom domain options, password protection for the inbox, and the ability to reply (a rare but valuable feature).
- Ad Intrusiveness: Many free services rely on ads. We penalized those with aggressive pop-ups, misleading download buttons, or auto-playing video ads that ruin the experience.
The “No Registration” Rule
A gold standard for true temporary email is that you should never have to create an account to use it. The moment a service asks for *its own* email to “save your inbox,” it ceases to be truly temporary and becomes just another data-harvesting operation. All tools on our list work on the “visit, get address, check inbox, forget” principle.
The Top 6 Temp Email Tools for 2026
After rigorous testing across dozens of services, these six consistently outperformed the rest for different user needs.
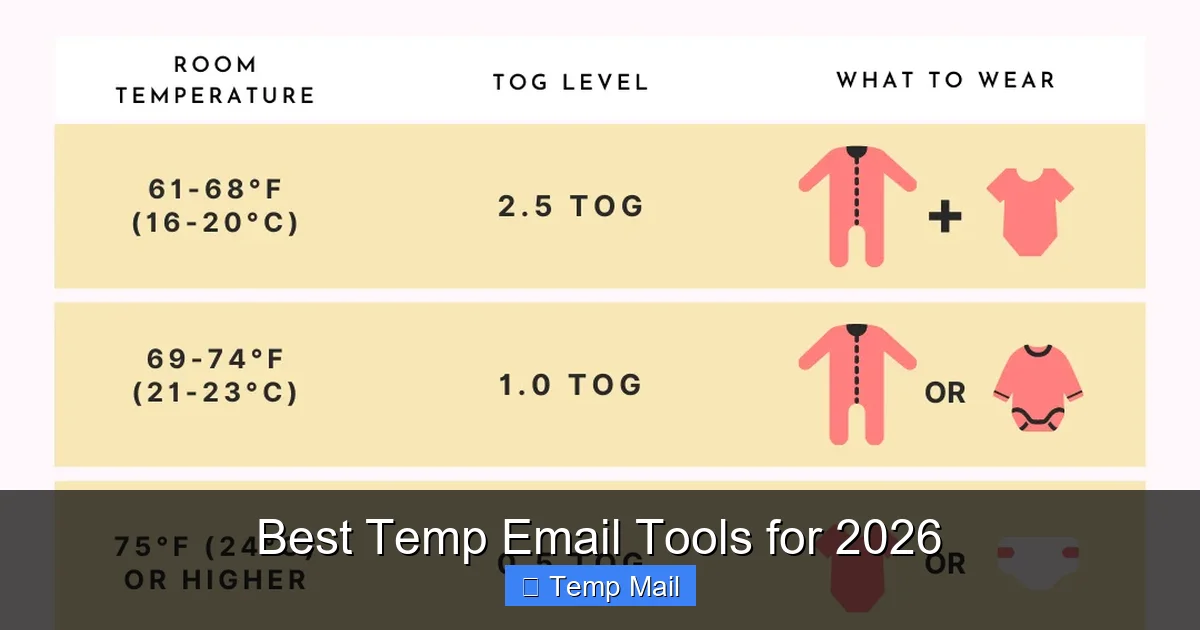
Visual guide about Best Temp Email Tools for 2026
Image source: thebabyway.co
1. SimpleLogin (by Proton): The Privacy Powerhouse
While technically an “email alias” service, SimpleLogin (now part of Proton) functions perfectly as a premium, long-term temp email solution and sets the benchmark for privacy in 2026.
Why It’s #1: It’s backed by Proton, the Swiss company famous for Proton Mail’s end-to-end encryption and strict privacy laws. Each alias is a real, forwardable email address that can be set to auto-delete after a certain number of messages or time. It offers a free tier with 10 aliases, and paid plans for unlimited. The browser extension is flawless, automatically detecting email fields and offering to generate an alias.
Best For: The privacy-conscious user who wants a more robust, slightly longer-term “temp” solution (weeks/months) with the option to reply and manage aliases from a dashboard. It’s the ethical choice for those who find traditional disposable mail too ephemeral.
Key Feature: Reply capability. You can actually reply from your alias, and it will forward through your real inbox (if you connect one) or via the SimpleLogin web interface. This bridges the gap between disposable and permanent.
2. Temp-Mail.org: The Speed Champion
When seconds count, Temp-Mail.org is the undisputed leader. Its entire design is optimized for one thing: getting you a working inbox and the verification code as fast as humanly possible.
Why It’s Fast: The site has minimal bloat. You land, get your random @temp-mail.org address, and the inbox is already open and polling. There’s no “waiting for email” animation; it just appears. The domain list is vast, so if one is blocked, you can switch with one click. Their dedicated mobile app (iOS/Android) is equally snappy.
Best For: Users in a hurry—signing up for a limited-time offer, verifying a phone number for a one-off service, or developers needing a quick email for automated tests.
Watch Out For: The free version has ads, but they are relatively non-intrusive display ads compared to the deceptive “download” buttons on some competitors. The inbox retention is short (usually 2-4 hours), which is by design for true temp use.
3. Guerrilla Mail: The Veteran with Character
One of the original disposable email services, Guerrilla Mail has evolved while keeping its quirky, no-nonsense identity. It’s reliable, has been around for over a decade, and offers a surprising amount of control.
Why It’s Trusted: Longevity breeds trust. It has survived privacy crackdowns and web changes. You can choose your inbox address from a list of random words (e.g., [email protected]), which is great for memorability in a short session. It also allows you to send a limited number of emails from the temporary address—a rare feature.
Best For: Users who want a bit more control over their temp address and might need to fire off a quick reply without revealing their real email. Also great for those who appreciate a service that doesn’t take itself too seriously but gets the job done.
Key Feature: Send a limited number of replies. You get about 3 “reply” credits per inbox, enough to respond to a confirmation or a simple query without using your real address.
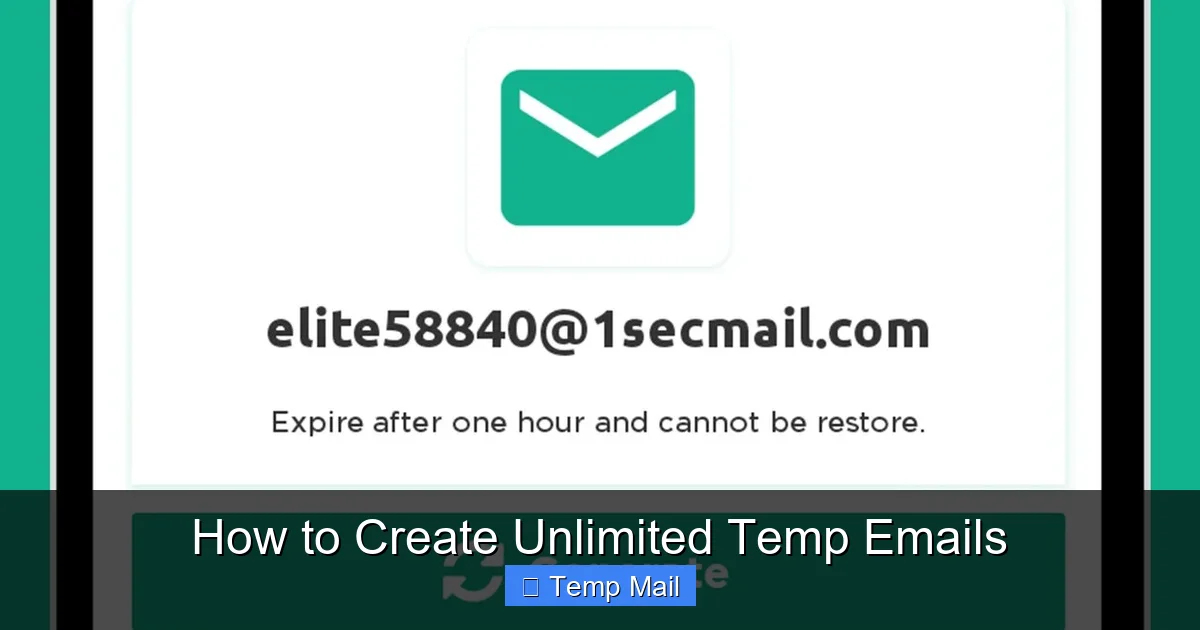
4. 10MinuteMail: The Classic, Focused Tool
As the name implies, this service is beautifully focused. You get a brand-new email address that is guaranteed to last for exactly 10 minutes, with a clear, large countdown timer. That’s it. No fuss, no extra features.
Why It’s Pure: Its simplicity is its strength. There’s no login, no account, no frills. The inbox is clean, ad-light, and solely dedicated to receiving mail for that 10-minute window. The domain is fixed (@10minutemail.com), so it’s easily recognized by most websites.
Best For: The ultra-cautious user who wants the shortest possible exposure and doesn’t want to think about settings. Perfect for a single, very quick verification where you’ll copy the code and abandon the tab immediately.
Limitation: The fixed 10-minute timer can be too short for some services that send emails with a delay. You have to be ready to act fast.
5. Maildrop: The Clean, Ad-Free Experience
Maildrop takes a different approach: it’s completely free and, remarkably, has no advertising whatsoever. It’s supported by donations and a paid “premium” tier that offers custom domains and longer retention.
Why It’s So Clean: The interface is minimalist and elegant, resembling a stripped-down Gmail. Inboxes are public by URL only (e.g., maildrop.cc/randomname), meaning you must save that URL to return. There is no search function on the free tier, which encourages you to use it for single, specific purposes.
Best For: Users who hate ads and are willing to trade a little convenience (no search, must save URL) for a pristine, distraction-free experience. Also good for shared temporary inboxes where you can give someone the URL.
Privacy Note: While ad-free, Maildrop’s privacy policy states they do not log IP addresses for free users, but they do scan for illegal content. It’s a solid middle-ground option.
6. Firefox Relay (by Mozilla): The Browser-Native Solution
For Firefox users, this is a game-changer. Firefox Relay is built directly into the browser (and available as a Chrome extension too). It generates a unique, random @relay.firefox.com address with one click in any email field.
Why It’s Integrated: No new tab, no new site. You’re on a sign-up page, click the Relay icon in your browser toolbar, and it fills the field. All emails are forwarded to your real Firefox account email with clear labels showing the Relay address used. You can block senders or disable the alias from your Relay dashboard.
Best For: Firefox (or Chrome) power users who want the ultimate in frictionless temp email use. It’s perfect for everyday, low-risk sign-ups where you want a buffer but might want to receive occasional updates (which you can block later).
Limitation: The free tier limits you to 5 aliases. The forwarding delay can sometimes be a few minutes. It’s less ideal for a “burn after reading” 10-minute scenario and more for a “manage this sender” scenario.
The Future of Temp Mail: AI, Integration, and Enhanced Privacy
Looking ahead to 2026 and beyond, temporary email is evolving from a simple utility to an intelligent privacy layer.
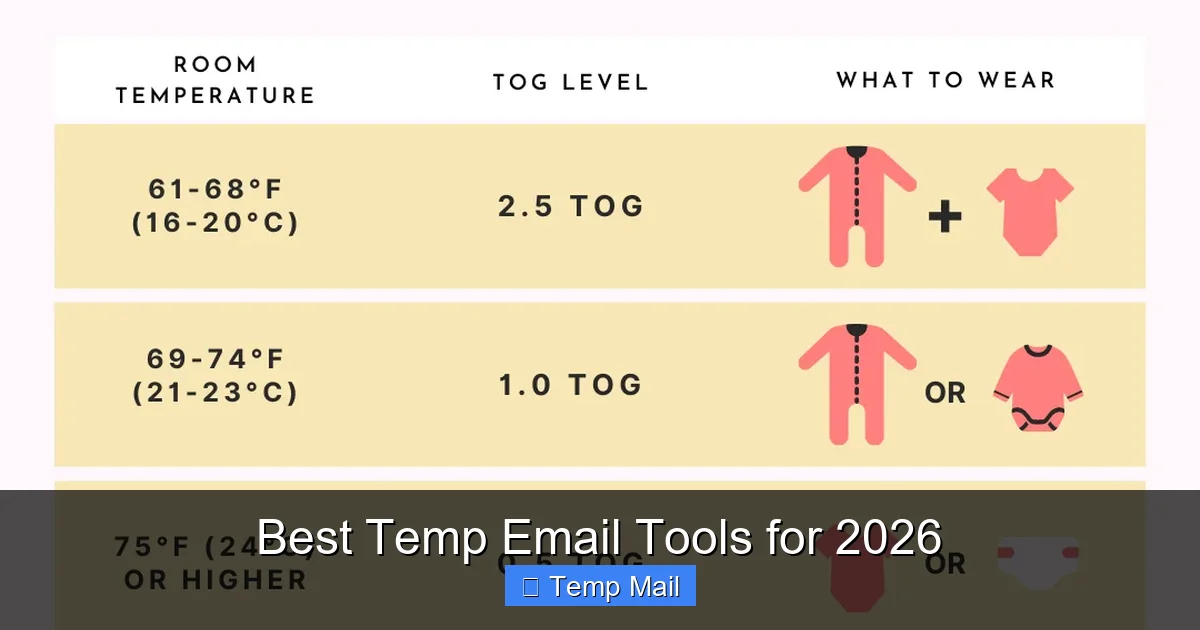
Visual guide about Best Temp Email Tools for 2026
Image source: thebabyway.co
AI-Powered Inbox Management
Imagine a temp email service that uses AI to read incoming messages. It can categorize them (“Verification Code,” “Newsletter,” “Promo”), auto-delete newsletters after 24 hours, and highlight the verification code in large text. Some experimental tools in 2025 already do this, and by 2026, it will be a standard premium feature.
Deep Browser & OS Integration
We’re moving beyond extensions. Expect native integrations into password managers (like Bitwarden or 1Password) that can generate and store temp aliases alongside your real credentials. Operating systems may include a privacy-focused “temporary identity” feature that auto-generates not just an email, but a pseudonymous name and address for forms.
Blockchain & Decentralized Identities
The cutting edge is using decentralized identifiers (DIDs) and blockchain-based systems. Instead of a random string @tempmail.com, you could prove you’re a unique human without revealing your email at all, using a cryptographic attestation. While nascent, this points to a future where the *concept* of an email for low-trust interactions may become obsolete.
Practical Guide: How to Use Temp Email Like a Pro in 2026
Having the tool is only half the battle. Using it effectively requires a strategy.
The Golden Rules
- Never use for: Banking, primary cloud accounts (Apple/Google/Microsoft), main social media, job applications, or any service where account recovery is critical. If you lose access to the temp inbox, you lose the account.
- Always check the domain list: Some sites block known disposable email domains. Have 2-3 different services bookmarked. If one domain is blocked, try another from the same service (e.g., switching from @temp-mail.org to @tmpmail.org).
- Copy the address immediately: Don’t rely on the browser tab. Copy the generated email address to your clipboard or a note app before navigating to the sign-up form.
- Keep the inbox tab open: Most services stop polling if you close the tab. Keep it open in the background and refresh periodically until you get the verification email.
- Use the “custom name” feature wisely: If a service offers it (like Guerrilla Mail), create a memorable name related to the site (e.g., [email protected]). This helps you identify which inbox is for what if you have multiple open.
Step-by-Step: Signing Up for a Sketchy Forum
Let’s walk through a real-world use case.
- Navigate to the forum’s registration page.
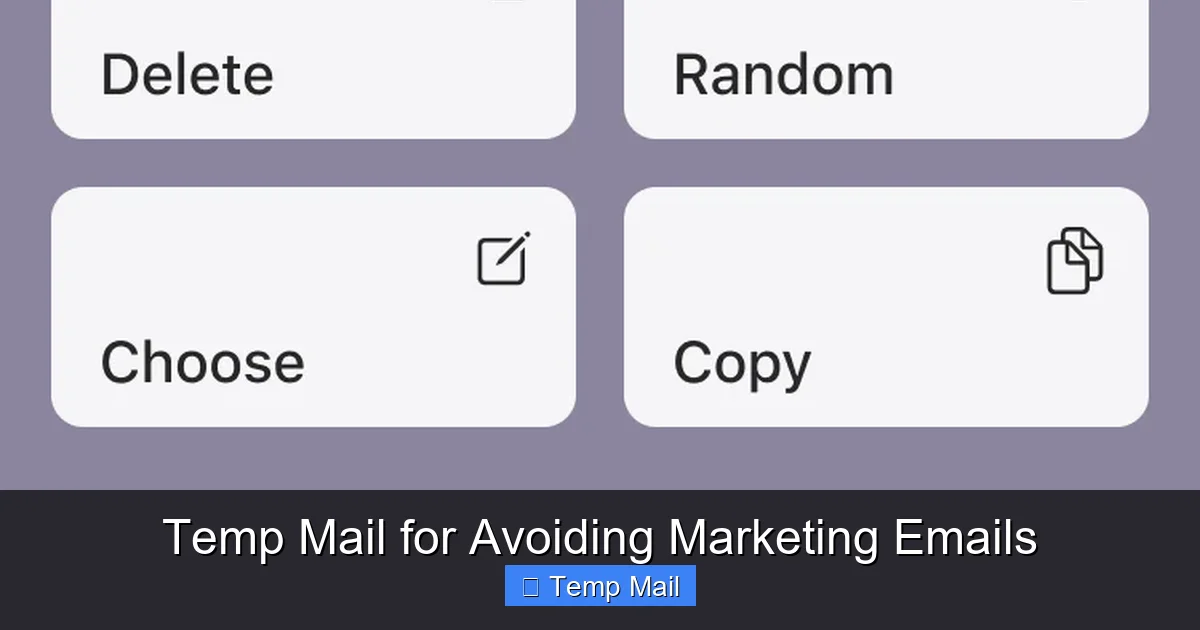
- Open a new tab and go to your preferred temp mail site (e.g., Temp-Mail.org).
- Your new address is generated instantly. Click the “Copy” button next to it.
- Return to the forum tab, paste the address into the email field, and fill in the rest of the form.
- Submit the form.
- Switch back to the temp mail tab. You should see “1 message” appear within 10-30 seconds. Click it to view.
- Find the verification link or code, copy it, and complete the forum activation.
- Once you’ve received the necessary email, you can close the tab. The inbox and its contents will vanish automatically.
When to Choose a Browser Extension vs. a Website
Choose a Browser Extension (Firefox Relay, SimpleLogin): For everyday, semi-regular use where you want frictionless protection. It’s faster and integrates into your workflow.
Choose a Standalone Website (Temp-Mail.org, Guerrilla Mail): For maximum anonymity (no browser fingerprinting linked to an extension), for one-off urgent tasks, or when you’re on a public/shared computer where installing extensions isn’t possible.
Conclusion: Your Inbox, Your Rules
The digital world of 2026 demands a new approach to identity. Handing out your primary email address is like giving out your home address to every stranger you meet for a coffee. It’s unnecessary and risky. Temporary email tools are the simple, effective lock on your digital front door.
Our top recommendations—SimpleLogin for privacy power users, Temp-Mail.org for raw speed, and Firefox Relay for seamless integration—represent the best of what the category offers. The right tool for you depends on your specific need: ultimate privacy, sheer velocity, or everyday convenience.
Start using one today. Bookmark a service, and the next time a website asks for an email you’re unsure about, default to your temp address. Take back control. Keep your primary inbox clean, your data private, and your online life compartmentalized. In the battle for digital privacy, a temporary email isn’t just a tool; it’s your first and most fundamental act of defense.
Frequently Asked Questions
Are temporary email services legal to use?
Yes, using a temporary email service is perfectly legal in most countries. They are legitimate privacy tools. However, using them to commit fraud, bypass bans, or violate a website’s Terms of Service can be illegal or result in account termination.
Can websites detect that I’m using a temporary email?
Yes, many websites maintain lists of known disposable email domains and will block sign-ups from those addresses. This is why services with large, frequently rotating domain pools (like Temp-Mail.org) are more effective. Using a unique alias service like SimpleLogin is harder to detect as it uses its own legitimate-looking domains.
What’s the difference between a “temporary email” and an “email alias”?
A traditional temporary email creates a completely separate, public inbox that expires. An email alias (like SimpleLogin or Firefox Relay) forwards all mail to your *real, permanent* inbox. Aliases last longer (you control them), allow replies, and are better for managing ongoing relationships (like newsletters) you may want to stop later without changing your real address.
What happens if I don’t check the temporary inbox in time?
The verification email will be deleted along with the entire inbox when it expires (typically after 10 minutes to 48 hours). You will not be able to activate the account or retrieve the code. You would need to generate a new temp email address and try the sign-up process again, if the website allows multiple attempts.
Do I need to install a browser extension to use these tools?
No, all the tools listed work perfectly as standalone websites. Browser extensions (like those from SimpleLogin or Firefox Relay) are a convenience feature that auto-fills email fields with a generated address, saving you a copy-paste step. They are optional but highly recommended for frequent users.
Can businesses use temporary email tools?
Businesses can use them for specific purposes like quality assurance testing, creating trial accounts for software evaluation, or for employees to sign up for industry newsletters without using corporate email. However, they should never be used for official business communications, customer accounts, or any process requiring legal accountability or audit trails.